Keyspace Technology
Product Overview
Cyber defense built to defend edge systems in real-time
Keyspace Technology (KST) is a new class of FPGA-based hardware-only cyber defense that protects the functional integrity of cyber-physical and high-value assets below where conventional cyber security can operate by enforcing trust at OSI Layers 1 through 4.
Conventional cyber security practices and tactics almost exclusively require prior knowledge of a system’s vulnerabilities. Regrettably, most vulnerabilities are identified only after an attack has occurred and only if it was discovered. Moreover, conventional cyber defense also has a near exclusive reliance upon software to succeed – either code in a machine or the character of a person – neither of which can be verified for integrity and reliability. This is where KST hardware differs: (KST Differentiation PP slide 12 detail)
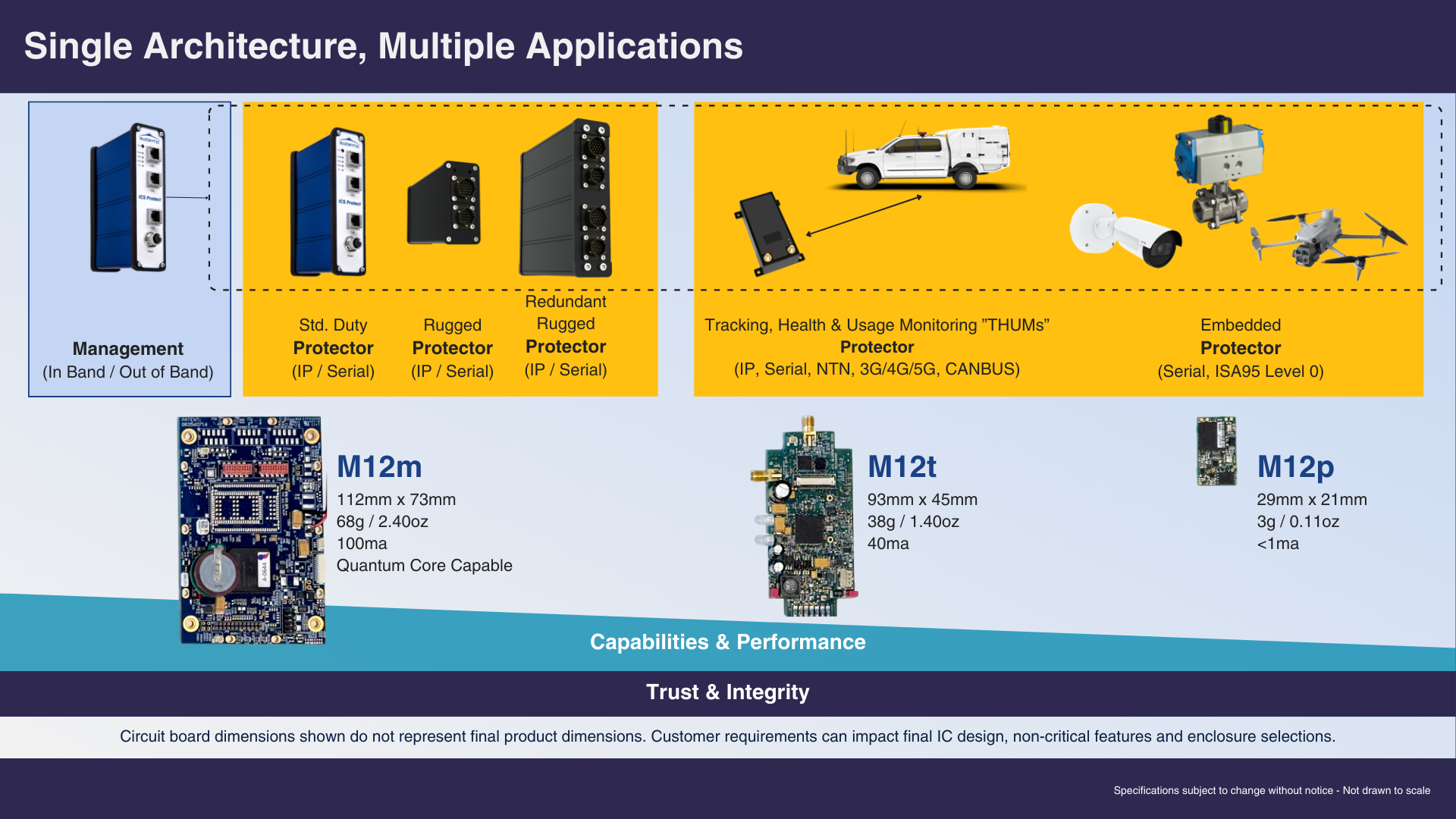
Applications
From satellites and ground stations to manufacturing facilities and public utilities to drones and autonomous vehicles – KST renders any connected system immune to all known and unknown cyber-attacks; including attacks mounted by AI and quantum computers.
Designed for use in harsh applications, KST enforces trust at the machine boundary. KST ensures that no signal enters any protected system unless it is structurally valid, behaviorally correct, and cryptographically verifiable.
Deployment is simple as KST requires no field maintenance or key management. Once configured for the customer environment any field service technician can install a KST device.
- Secures OSI Layer 1-4 (ISA95 Level 0 Capable)
- Packet-level Authentication and Encryption
- Flexible Connectivity: Serial, Analog/Digital I/O, IP, Wi-Fi, RF, Satellite
- 100% Hardware Single Function System
- Advanced Post-Quantum Symmetric Encryption
- No Key Management
- No Maintenance